VaultLine is not designed as a collection of independent services. It is designed as a coordinated system where integrity is maintained through the interaction of multiple layers. Each layer exists with a clear responsibility, but no layer operates in isolation. The system works because these layers continuously reinforce one another — ensuring that correctness, traceability, and recoverability are preserved at all times. The goal is not just to process operations. The goal is to ensure that every operation results in a state the system can trust.Documentation Index
Fetch the complete documentation index at: https://docs.vaultline.dev/llms.txt
Use this file to discover all available pages before exploring further.
From Concepts to System
VaultLine begins with a set of foundational ideas: System Integrity. Failure-First Design. Recoverability. Auditability. These are not abstract principles written for documentation. They directly shape how the system is built. Each concept manifests as a structural component within the architecture. The system is, in many ways, a physical expression of these ideas. Integrity is not enforced after execution. It is embedded into the system’s design.High-Level Architecture
- State is always consistent
- Failures are recoverable
- System behavior is fully traceable
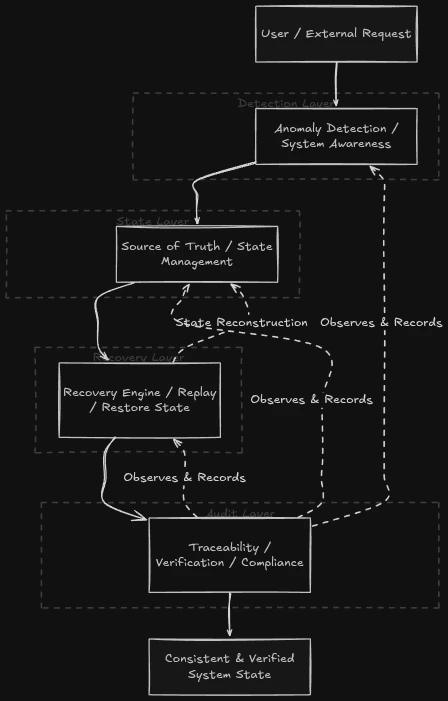
At a high level, VaultLine can be understood as a sequence of coordinated layers through which every request flows. But more importantly, it is a system where these layers continuously observe, validate, and support one another.
Layered Design
The architecture of VaultLine is organized into four primary layers. Each layer represents a distinct responsibility, but their real strength lies in how they interact.Detection Layer
The detection layer is responsible for awareness. Every incoming request, signal, or system interaction passes through a layer that continuously evaluates behavior. It looks for irregularities, anomalies, and patterns that may indicate risk or inconsistency. This is not simply about identifying fraud or errors. It is about ensuring that the system is never blind to its own state. A system that cannot observe itself cannot maintain integrity.State Layer (Ledger)
At the core of the system lies the state layer — the ledger. This layer acts as the single source of truth for everything that happens within VaultLine. Every meaningful action results in a state transition that is recorded, preserved, and made consistent. The purpose of this layer is not just storage. It is to ensure that the system always has a clear and reliable understanding of its current state. Without a trustworthy state, no system can guarantee correctness.Recovery Layer
The recovery layer exists because failure is not hypothetical. It is expected. Rather than reacting to failure after it occurs, VaultLine continuously prepares for it. At every stage of processing, the system maintains the ability to identify a correct state and return to it if needed. Recovery is not improvisation. It is a predefined capability. This layer ensures that even if something goes wrong, the system can restore correctness in a predictable and controlled manner.Audit Layer
The audit layer provides visibility and trust. Every action within the system is recorded in a way that allows it to be understood, traced, and verified. This is not limited to capturing events — it is about preserving context and relationships between them. The system is always capable of answering: What happened? Why did it happen? How did it affect the system? This layer ensures that the system is not just correct — it is explainable.How the Layers Interact
A request moving through VaultLine is not simply processed. It is continuously evaluated, recorded, and prepared for recovery. A typical flow begins with a request entering the system, where it is first observed by the detection layer. The system evaluates the request in context, ensuring awareness from the very beginning. As the request progresses, it reaches the state layer, where the system records the resulting state transition. This ensures that the system always maintains a consistent and reliable representation of itself. At the same time, the recovery layer ensures that this transition can be reversed or reconstructed if necessary. The system is never in a position where it cannot return to correctness. Throughout this entire process, the audit layer records the full context of what is happening. Every step is traceable. If a failure occurs at any point, the system does not enter an undefined state. It identifies the last correct state, reconstructs the required sequence of events, and restores consistency — all while maintaining a complete trace of what occurred.Why This Architecture Works
Most systems are designed to function under ideal conditions and respond to failure when it occurs. VaultLine is designed differently. It assumes that failure will happen and builds the system in a way that ensures failure does not compromise correctness. This architecture works because:- Awareness is continuous
- State is reliable
- Recovery is prepared
- Behavior is traceable