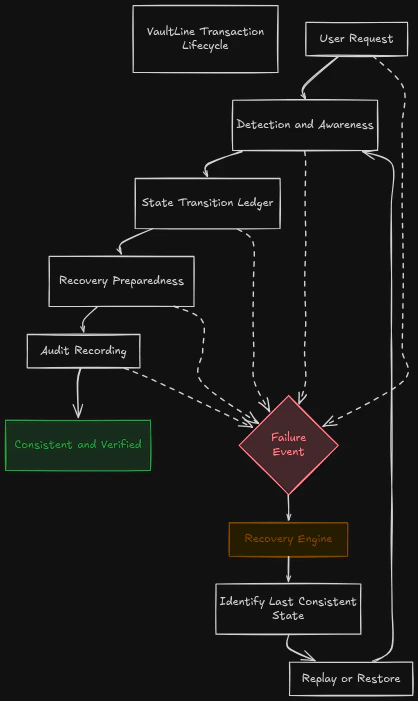
A system is not defined by what it claims to do. It is defined by how it behaves when something actually happens. The transaction lifecycle in VaultLine represents the complete journey of a request as it moves through the system — from entry to final state. More importantly, it reflects how the system maintains correctness, traceability, and recoverability at every step of that journey. This is not just a processing pipeline. It is a controlled and observable progression of state.Documentation Index
Fetch the complete documentation index at: https://docs.vaultline.dev/llms.txt
Use this file to discover all available pages before exploring further.
From Request to State
Every interaction with VaultLine begins with a request.Transaction Flow
- Understood
- Evaluated
- Recorded
- Recoverable
Entry and Detection
As a request enters the system, it first passes through a layer of continuous observation. This stage is not about blocking or allowing actions in a simplistic sense. It is about understanding context — identifying whether the request aligns with expected system behavior or introduces potential inconsistencies. The system evaluates signals, patterns, and relationships in real time. At this point, nothing has been committed. The system is still in a state of awareness.State Transition
Once the system has sufficient confidence in the request, it proceeds to update its internal state. This is where the system moves from evaluation to commitment. The state layer ensures that every transition is:- Clearly defined
- Consistent with prior state
- Recorded as a reliable representation of truth
Recovery Preparedness
At the moment a state transition occurs, the system is already prepared for the possibility of failure. This is a defining characteristic of VaultLine. The system does not wait for something to go wrong before considering recovery. Instead, it ensures that every action carries with it the ability to be:- Reconstructed
- Replayed
- Restored
Continuous Audit
Throughout the entire lifecycle, the system maintains a complete and contextual record of what is happening. Every action is captured as part of a broader sequence, not as an isolated event. This enables the system to:- Reconstruct the full chain of events
- Explain why decisions were made
- Verify outcomes against recorded behavior
Behavior Under Failure
Failure is not treated as a disruption to the lifecycle. It is treated as a condition the system is designed to operate within. If a failure occurs during processing, the system does not enter an undefined state. Instead, it:- Detects the inconsistency
- Identifies the last correct state
- Reconstructs the necessary sequence of actions
- Restores the system to a consistent condition
Final State
Every request results in a state. In VaultLine, that state is not considered complete until it meets three conditions:- It is consistent
- It is recoverable
- It is fully traceable
A Controlled System, Not a Reactive One
Traditional systems often process requests and deal with consequences later. VaultLine operates differently. At every stage of the lifecycle, the system is:- Observing
- Validating
- Recording
- Preparing for recovery